What is SQL Injection?
SQL injection (SQLi) is a code injection technique that exploits vulnerabilities in applications that build SQL queries using unsanitized user input. When an application directly concatenates user input into database queries, attackers can manipulate the query structure to access unauthorized data or perform malicious operations.
Understanding the mechanics of SQL injection helps you identify vulnerable code and craft effective defenses. Here's the typical attack flow:
1. Identify injection points, attacker finds input fields that interact with the database: login forms, search boxes, URL parameters2. Test for vulnerability insert special characters like single quotes (') to see if they cause database errors
3. Determine database structure, use error messages or techniques like UNION SELECT to discover table names and columns
4. Extract or manipulate data, raft payloads to dump sensitive data, modify records, or escalate privileges
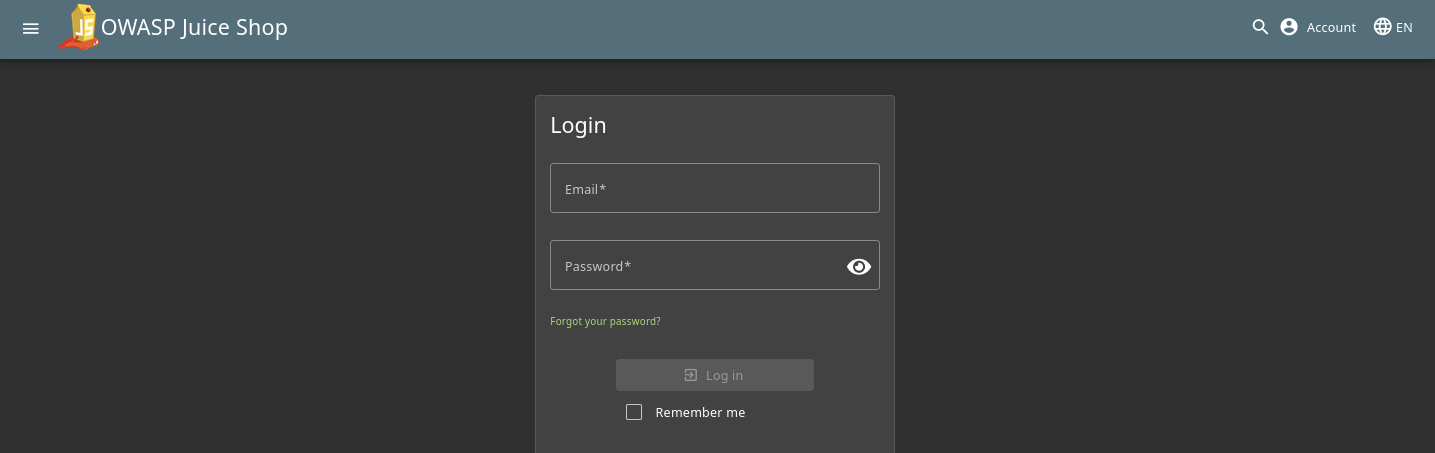
Here we will identify injection points, I want to use this login forum to try and get an admin account.
First lets try to see if sql injection is even possible by imputting ' in the username and just anything in the password field to see if it says anything weird. If you get anything similar to [Object] [Object] or honestly anything that isn't invallid username/password.
For this excersize I already know the login forum is vulnerable to SQLi so I'm going to to try and bypass the password being required.
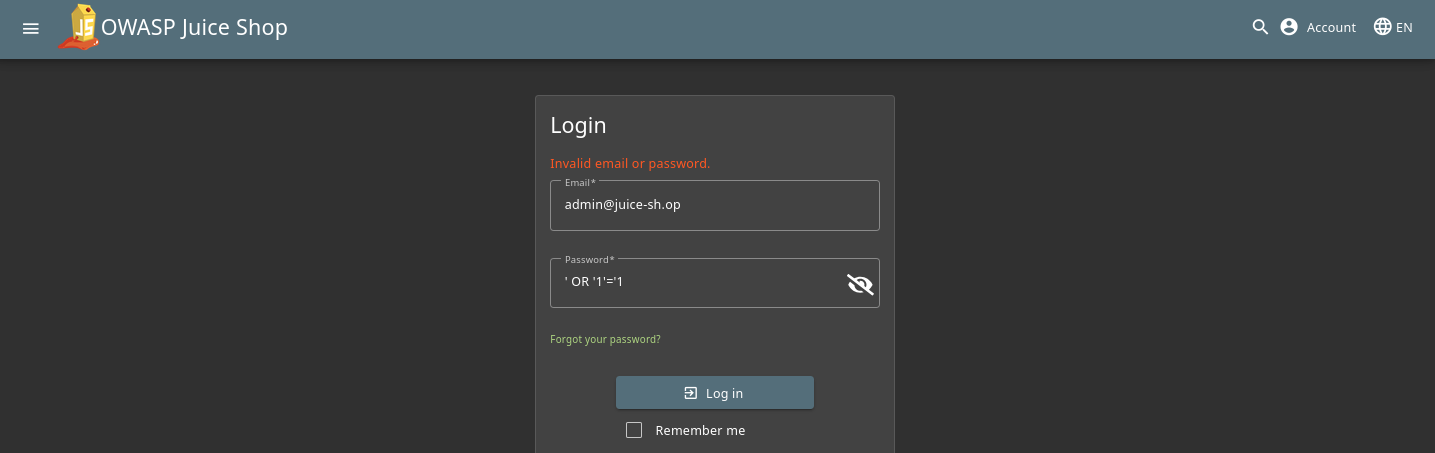
Here we will put the email in like normal and instead of a password we will try ' OR '1'='1
If a user enters ' OR '1'='1 as the password, the resulting query inside the database becomes: SELECT * FROM users WHERE username = 'admin' AND password = '' OR '1'='1' Since '1'='1' is always true, this query returns all users, effectively bypassing authentication entirely.
After imputing that it still says invalid username or password so we may not be able to inject anything in the password section, lets try and do a different approach and work in the username section only.
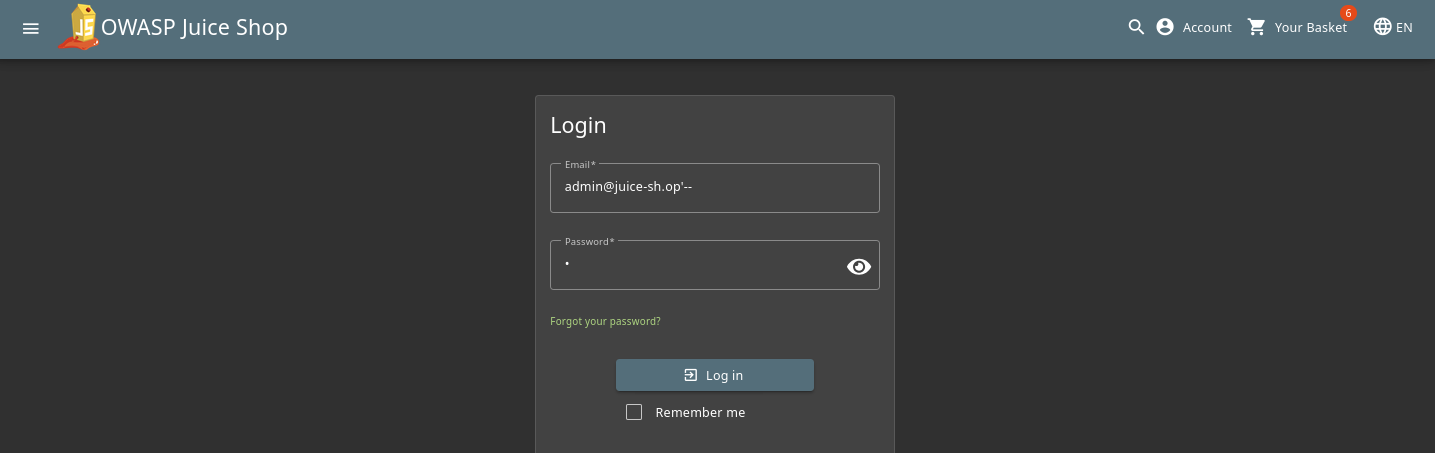
Here we modified the email and added '-- at the end of it, with this code if the database reads it, it should bypass the requirment for a password all together and just let us in with only the username.
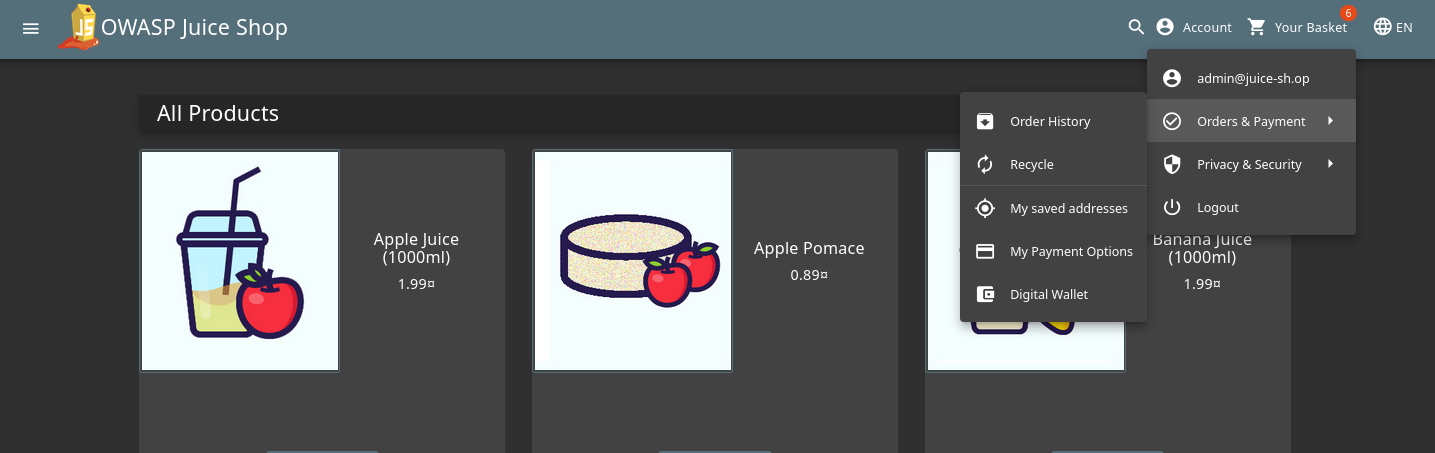
And there we go! We were able to bypass the need for a password and get into the admin account of this website. Congrats!