Cross Site Scripting
Cross-Site Scripting (XSS) is a vulnerability that allows attackers to inject malicious scripts into web pages viewed by other users. Here are the main types of XSS:
Stored XSS: The malicious script is stored on the target server (e.g., in a database) and served to users.
Reflected XSS: The script is reflected off a web server, executed immediately without being stored persistently.
DOM-based XSS: The attack reflects and executes within the client's browser, manipulating the Document Object Model (DOM).
Self-XSS: The victim is tricked into executing scripts in their browser console, often through social engineering.
Blind XSS: The attacker does not see the results of the attack directly, as the payload is stored and executed later.
Today we will just show a simple DOM based XSS attack on a private network that I have full permission to hack.
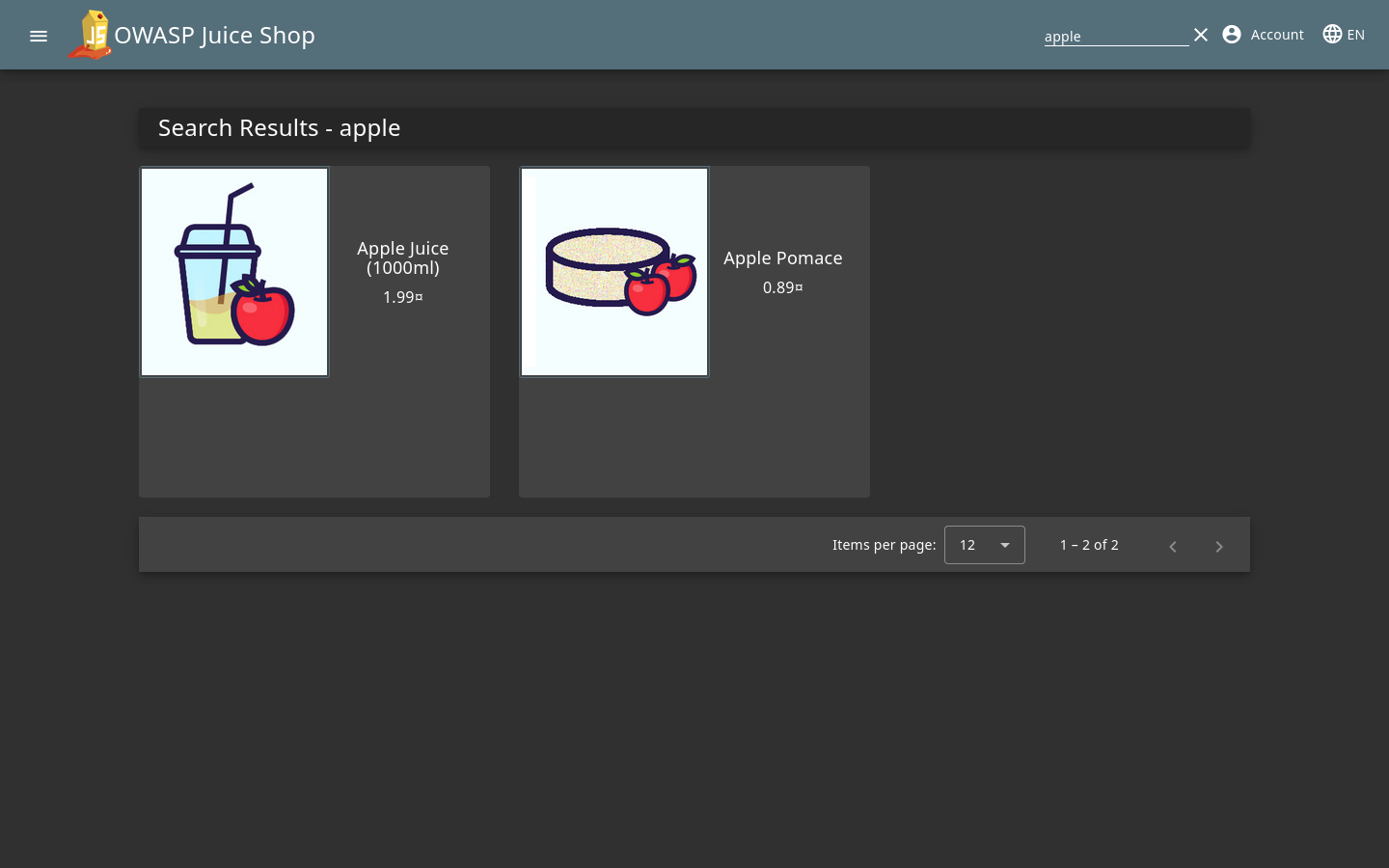
If you look in the top right it seems like anything we search for will apear in a box that says "Search Results - whatever you searched". This seems like it may be a good spot for XSS. Lets run a test real quick to check.
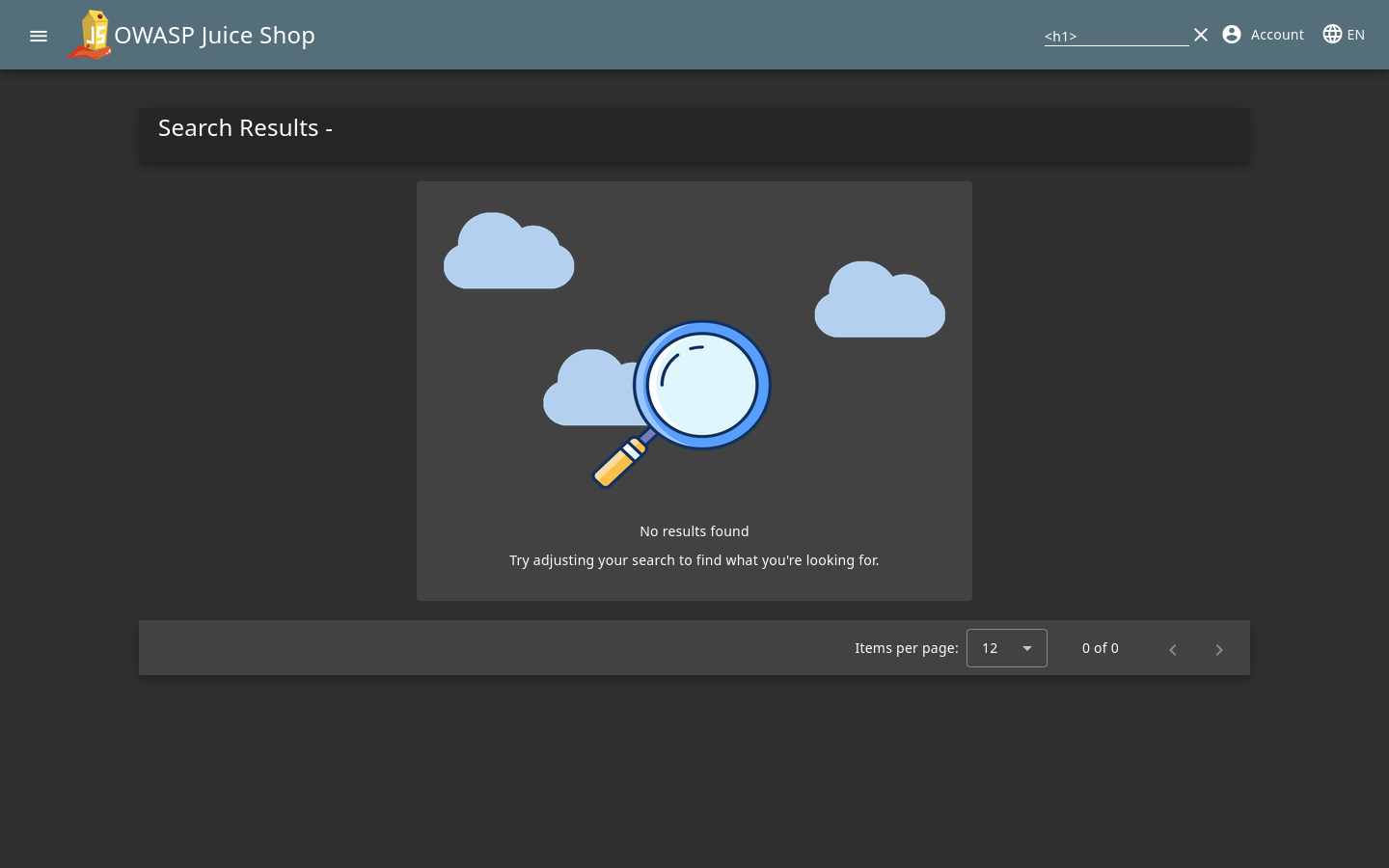
Notice how nothing showed up after the Search Results - ? well that could mean that the h1 tag was imbedded into the site, let's try and see if we can inject some code in it by typing a simple script "iframe src="javascript:alert(`xss`)" (add < and > to the beginning and end to make it work) and see what happens.
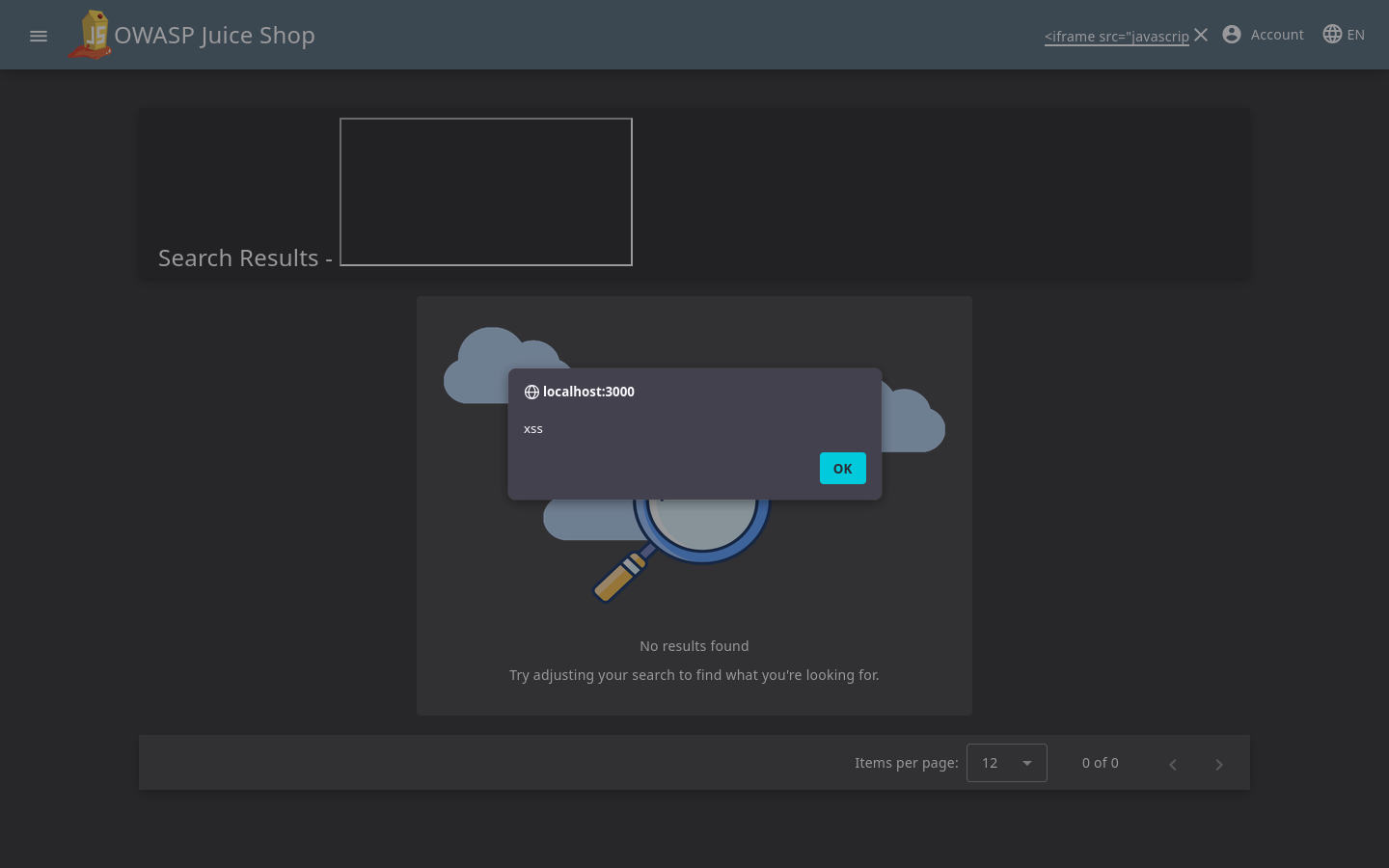
And with that we can sucessfully inject javascript into the webpage to output whatever text we want! With a basic understanding of javascript you could inject code to do a varity of things that I can't legally get into here.